Martijn Russchen
2024-04-25 14:00:00
www.hackerone.com
You can now streamline and enhance your vulnerability management process with HackerOne’s in-platform GenAI copilot, Hai. Hai delivers a deeper and more immediate understanding of the reports that come in, helping you make decisions and deliver fixes faster by effortlessly translating natural language into precise queries, enriching vulnerability reports with additional relevant context, and utilizing platform data to generate insightful recommendations. Incorporating AI’s capabilities into your workflows strengthens the ever-evolving security processes in a constantly changing world of cyber threats.
Hai is now generally available for all HackerOne customers. Use Hai to:
- Strengthen Understanding: Hai decodes complex reports, providing succinct summaries and detailed visual analyses, fast-tracking your team’s understanding and response capabilities.
- Improve Communication: Hai acts as a communication bridge, clarifying technical details and remediation steps, enabling seamless collaboration between security, development teams, and hackers.
- Accelerate Remediation: Hai streamlines find-to-fix cycles with targeted insights and personalized advice, optimizing remediation and harnessing unique business knowledge for faster, smarter action.
- Streamline your SDLC: Hai elevates your SDLC, offering custom vulnerability scanner templates, seamless API integration, and dynamic automation for faster, smarter security processes.
Strengthen Understanding
Navigating and interpreting complex security reports is time-consuming, often delaying critical response actions and decision-making within teams.
Whether faced with intricate reports, complex proofs of concept, or technical details, Hai provides easily understandable explanations of vulnerabilities.
You can ask Hai for help with:
- Report summarization
- Remediation advice
- Content generation (comments/acknowledgments)
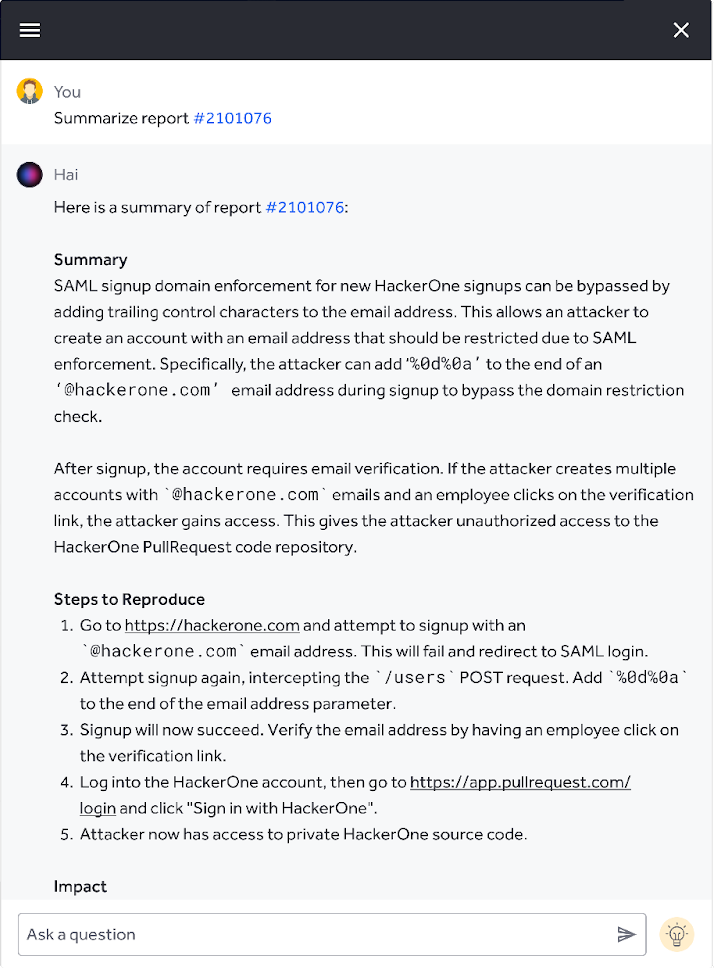 |
“In my role, I’ll help customers review reports and understand the impact. And sometimes we’ll get a report that is very long, like 30 steps. These reports can take at least 10 minutes to comprehend. In these scenarios, I’ve found Hai to be incredibly useful for asking questions about the report and understanding its impact.”
— Dane Sherrets, Senior Solutions Architect, HackerOne
Improve Communication
So much of a vulnerability’s story is in the proof of concept. With Hai, you can extract actionable insights and details from visuals like screenshots to speed up vulnerability analysis and plan for remediation. With support for screenshot analysis, you can:
- Get concise explanations of what’s depicted in images.
- Ask Hai to pull specific information from visuals, such as HTTP requests or response IDs.
- Have Hai convert information from images into usable formats, e.g. cURL commands.
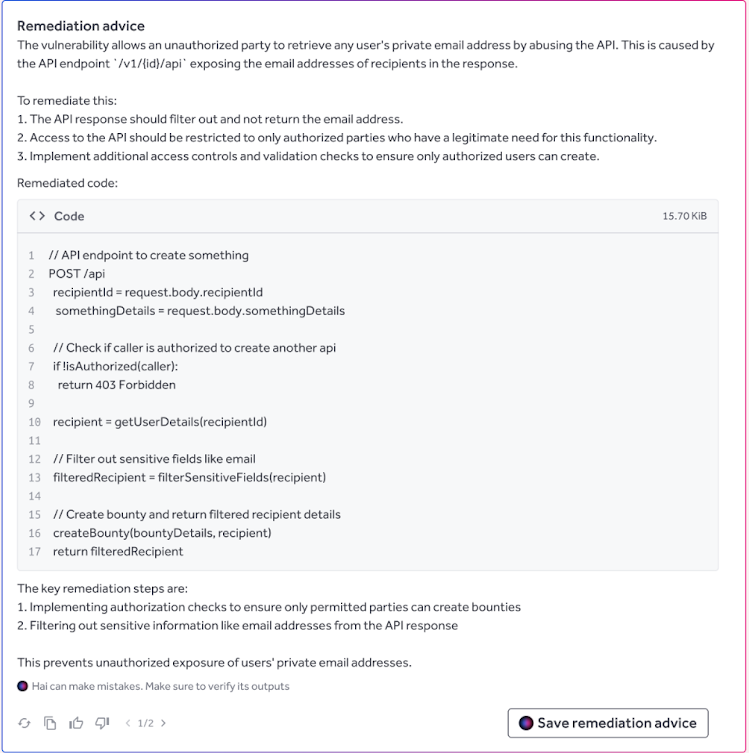
Accelerate Remediation
Navigating vulnerability remediation requires teams to align strategies with unique business requirements, often causing delays and inefficiencies in addressing security issues.
Determine the best approach to fixing vulnerabilities by analyzing them with Hai, enriching reports with relevant context, and receiving personalized remediation advice.
- Hai can help edit vulnerability reports by suggesting a title, updating CVSS ratings, or recommending a vulnerability class from the CWE database.
- Quickly shorten an essay or change your tone of voice with in-workflow writing assistance.
- Maintain your own curated knowledge base so Hai can become a hivemind of valuable information specific to your organization.
Streamline Your SDLC
Teams struggle with the manual repetition of tasks and lack customized solutions that align with their specific domain knowledge and operational needs.
Create personalized plays for repetitive tasks, providing custom instructions to teach Hai your organization’s domain knowledge.
- Go deeper on remediation advice by teaching Hai more about your tech stack and processes.
- Structure a vulnerability report by extracting common parameters, such as endpoint, exploit URL, payload, etc.
Leverage the Hai API
Organizations face challenges in integrating advanced AI capabilities into their vulnerability management processes to automate tasks, initiate proactive incident responses, and manage data efficiently.
Access Hai via the HackerOne API to easily integrate its features into your current processes and tools.
- Unlock task automation and accelerate internal workflows through dynamic, programmatic interaction with Hai.
- Proactively initiate incident response for sensitive data, like PII, found in proofs of concept.
- Efficiently extract, transform, and query business-specific information for internal escalation and routing, enhancing operational agility.
“Hai has significantly reduced the time my team spends sifting through bug reports or creating responses, allowing us to focus more on resolving and communicating vulnerabilities quickly.”
— Alexander Hagenah, Head of Cyber Controls at SIX Group
HackerOne customers, including Salesforce, SIX, Zoom, Adobe, and Hyatt, are already using Hai to optimize their vulnerability management processes.
“With Hai API, you have the ability to generate an API token that can be used to query Hai and use it on specific reports or use it programmatically. As soon as a report is received, it marks a custom field or routes it to the relevant team. There’s still a human in the loop ensuring Hai is behaving as intended, but I’ve seen 100% success rate of doing it this way.”
— Dane Sherrets, Senior Solutions Architect, HackerOne
To learn how Hai can help your organization stay ahead of evolving threats, contact us today and speak with a security expert. If you’re a HackerOne customer and want to experience Hai, read here how to opt in.
Support Techcratic
If you find value in our blend of original insights (Techcratic articles and Techs Got To Eat), up-to-date daily curated articles, and the extensive technical work required to keep everything running smoothly, consider supporting Techcratic with Bitcoin. Your support helps me, as a solo operator, continue delivering high-quality content while managing all the technical aspects, from server maintenance to future updates and improvements. I am committed to continually enhancing the site and staying at the forefront of trends to provide the best possible experience. Your generosity and commitment are deeply appreciated. Thank you!
Bitcoin Address:
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge
Please verify this address before sending any funds to ensure your donation is directed correctly.
Bitcoin QR Code
Your contribution is vital in supporting my efforts to deliver valuable content and manage the technical aspects of the site. To donate, simply scan the QR code below. Your generosity allows me to keep providing insightful articles and maintaining the server infrastructure that supports them.

Privacy and Security Disclaimer
- No Personal Information Collected: We do not collect any personal information or transaction details when you make a donation via Bitcoin. The Bitcoin address provided is used solely for receiving donations.
- Data Privacy: We do not store or process any personal data related to your Bitcoin transactions. All transactions are processed directly through the Bitcoin network, ensuring your privacy.
- Security Measures: We utilize industry-standard security practices to protect our Bitcoin address and ensure that your donations are received securely. However, we encourage you to exercise caution and verify the address before sending funds.
- Contact Us: If you have any concerns or questions about our donation process, please contact us via the Techcratic Contact form. We are here to assist you.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.

















































![2024 Upgrade Tesla Model Y Sunshade Roof [Never Sag, No Gaps, Nano Ice-Crystal Coatings]…](https://techcratic.com/wp-content/uploads/2024/11/61USyoncEvL._AC_SL1500_-360x180.jpg)









![Japanese Movie – The X From Outer Space (Uchu Dai Kaijyu Girara) [Japan BD] SHBR-263](https://techcratic.com/wp-content/uploads/2024/11/81rV3BDVGJL._SL1024_-360x180.jpg)








