Naz Bozdemir
2024-04-09 12:00:04
www.hackerone.com
- Effectiveness: Effectiveness measures the method’s ability to provide reliable and accurate vulnerability detections, comprehensive system coverage, compliance with standards, and a diverse testing team for nuanced perspectives.
- Speed: Efficiency concerns the method’s operational benefits, such as the ease and rapidity of obtaining pentesting services, the immediate delivery of results and analytics, continuous and transparent communication, and effortless SDLC integration.
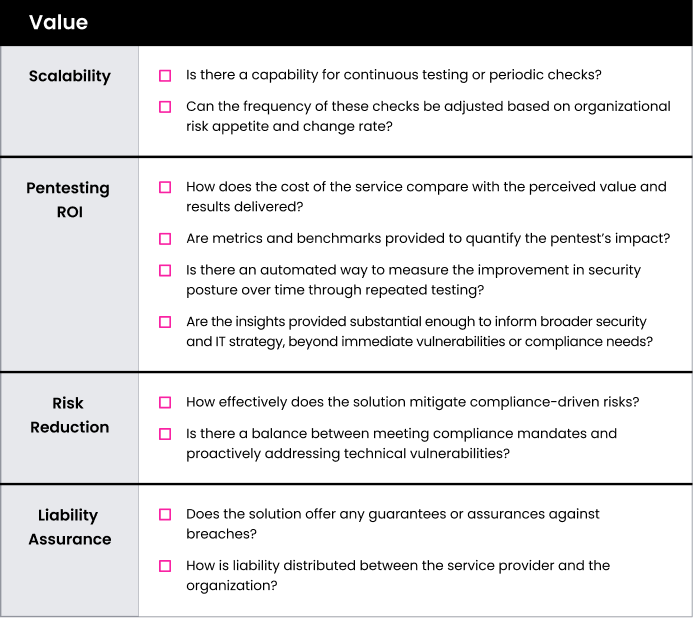
- Value: Value explores the method’s ROI, focusing on scalability, both tangible and intangible outcomes from pentesting efforts, and its success in risk mitigation.
With these categories in mind, let’s explore the “Value” factor more closely and see how each security testing alternative measures up.
Pentesting Options
The landscape of security testing is diverse, where players offer a variety of methodologies and pentesting options that cater to different organizational needs. Understanding these methods is crucial for selecting the pentesting strategy that best fits your security needs, but it’s not an easy task. Here are the primary pentesting methods currently in use:
- Traditional Pentesting via Consultancies: Pentesting services are delivered by professional service providers, primarily leveraging their in-house salaried pentesters or long-term contractors.
- Traditional Pentest as a Service (PTaaS): Essentially, traditional pentesting with an added user interface.
- Community-driven Pentest as a Service (PTaaS): A modern evolution of pentesting, harnessing the collective expertise of a global community of vetted security researchers.
- Automated Pentesting: Including autonomous approaches powered by generative AI (GenAI) algorithms and advanced machine learning models, uses predefined scripts or tools to systematically scan and assess systems for vulnerabilities based on recognized signatures or patterns.
The Problem With Pentest Value
Pentesting has been around for decades, but it hasn’t undergone the revolution that other security practices have. Organizations tend to rely on pentesting as a tool to just “check-the-box” for compliance, rather than something that actually protects their brand and customers. Traditional pentesting engagements are slow, take up excessive bandwidth, and don’t deliver impactful results.

Security leaders are challenged to show their stakeholders the value of pentesting against its cost. But what are the factors that contribute to the value of an effective pentest, and how can security teams measure them?
Measuring Pentest Value
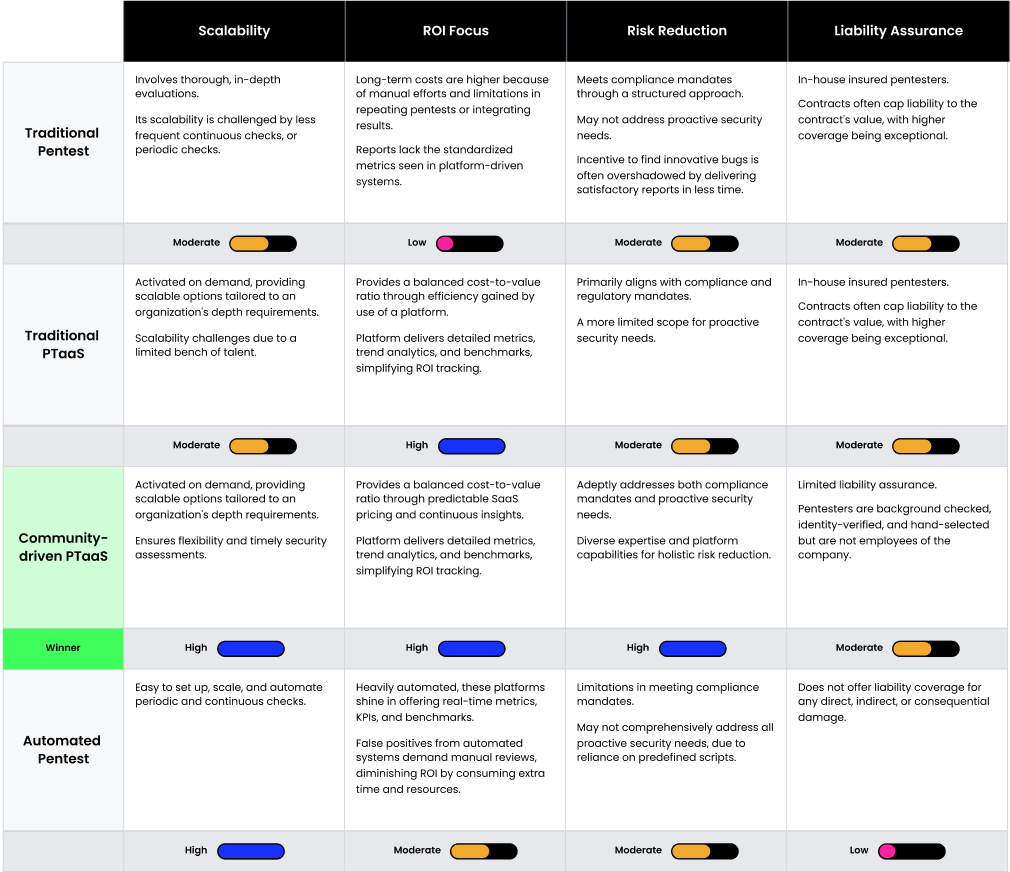
In evaluating the following, keep in mind that the impact of each pentesting method varies based on its application, the caliber of expertise involved, and the precise goals underpinning the test objectives.
- Scalability: Indicates the adaptability of the testing process to different scales, whether expanding for larger systems or being precise for specific areas
- ROI Focus: Measures the return on investment (ROI) derived from the pentesting process, highlighting the tangible and intangible benefits against the incurred costs
- Risk Reduction: Discerns whether the solution is geared toward meeting compliance and regulatory mandates, addressing proactive security needs, or both
- Liability Assurance: Addresses the potential legal and financial implications of security breaches and how the pentesting solution provides a safety net against such contingencies
Our methodology evaluates different pentesting approaches against key dimensions of effective security testing, using a scale of Low to High. While the results do highlight a preferred method, it’s essential to understand that our scoring system reflects the general attributes of each security testing type. The actual value of an approach may vary based on business priorities, technology stack, and other unique factors. As you interpret the findings, remember that Value is only one of three factors, and it may or may not resonate most with your specific business objectives.
The elements addressed above underscore the depth, precision, and thorough nature of a modern pentesting alternative, ensuring a structured and methodology-driven assessment of an organization’s security posture.
“When your compliance people don’t have a real deep understanding of security, they don’t understand how to take advantage of something like a penetration test. They’re looking for a checkbox to be filled because they have other things to do with their day. We’d really like these things to be more valuable to people outside of security. And so these are the things GigaOm is looking for when reviewing vendors, and our criteria has changed because the market is evolving, and it’s evolving in a really positive way. We’re still experiencing a significant upswing in value from PTaaS services as these services have it all.”
— Howard Holton, CTO of GigaOm
Security Testing Value Evaluation Matrix
This checklist can be used to evaluate the speed of each of the four security testing options: traditional pentesting, Traditional PTaaS, community-drivenPTaaS, and automated pentesting.
The Power of PTaaS With HackerOne
When scoring against Effectiveness, Quality, and Value, PTaaS stands out as a flexible approach that can adapt to an organization’s specific needs, and is priced accordingly. Community-driven PTaaS is the premier choice for comprehensive testing combined with in-depth analysis, all while ensuring a swift setup and completion of the assessment.
“Although hackers don’t have a view into how the business works, that’s part of the reason you want to use somebody with an external perspective. PTaaS gives you that multi-perspective view and really takes a broad look at your network, meaning you’re leveraging your funds to the best of your ability, rather than just meeting a compliance need. it’s a different method to go about trying to determine whether your organization is safe or not.”
— Howard Holton, CTO of GigaOm
HackerOne Pentest transcends routine compliance checks, delivering in-depth insights, efficiency, and actionable results tailored to your business and security needs. If you’re ready to learn more about how PTaaS measures up in other criteria, download the eBook: The Pentesting Matrix: Decoding Modern Security Testing Approaches. Or, tell us about your pentesting requirements, and one of our experts will contact you.
Support Techcratic
If you find value in our blend of original insights (Techcratic articles and Techs Got To Eat), up-to-date daily curated articles, and the extensive technical work required to keep everything running smoothly, consider supporting Techcratic with Bitcoin. Your support helps me, as a solo operator, continue delivering high-quality content while managing all the technical aspects, from server maintenance to future updates and improvements. I am committed to continually enhancing the site and staying at the forefront of trends to provide the best possible experience. Your generosity and commitment are deeply appreciated. Thank you!
Bitcoin Address:
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge
Please verify this address before sending any funds to ensure your donation is directed correctly.
Bitcoin QR Code
Your contribution is vital in supporting my efforts to deliver valuable content and manage the technical aspects of the site. To donate, simply scan the QR code below. Your generosity allows me to keep providing insightful articles and maintaining the server infrastructure that supports them.

Privacy and Security Disclaimer
- No Personal Information Collected: We do not collect any personal information or transaction details when you make a donation via Bitcoin. The Bitcoin address provided is used solely for receiving donations.
- Data Privacy: We do not store or process any personal data related to your Bitcoin transactions. All transactions are processed directly through the Bitcoin network, ensuring your privacy.
- Security Measures: We utilize industry-standard security practices to protect our Bitcoin address and ensure that your donations are received securely. However, we encourage you to exercise caution and verify the address before sending funds.
- Contact Us: If you have any concerns or questions about our donation process, please contact us via the Techcratic Contact form. We are here to assist you.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.
















































![2024 Upgrade Tesla Model Y Sunshade Roof [Never Sag, No Gaps, Nano Ice-Crystal Coatings]…](https://techcratic.com/wp-content/uploads/2024/11/61USyoncEvL._AC_SL1500_-360x180.jpg)










![Japanese Movie – The X From Outer Space (Uchu Dai Kaijyu Girara) [Japan BD] SHBR-263](https://techcratic.com/wp-content/uploads/2024/11/81rV3BDVGJL._SL1024_-360x180.jpg)








