Chris Campbell
2024-01-18 12:05:58
www.hackerone.com
As a result, it’s only natural that code gets shipped with security flaws. Thankfully, many organizations have solutions in place to catch security vulnerabilities after code is shipped, like pentesting and bug bounty programs. Of course, it’s much cheaper for organizations to use ethical hackers to identify vulnerabilities than it is for them to undergo a breach. But wouldn’t it be cheaper yet if these vulnerabilities were found and resolved from the source code directly — without interfering with the DevOps process?
Find Mistakes Earlier
HackerOne Code Security Audit provides a means to address the concern of critical vulnerabilities by leveraging a community of vetted, expert code reviewers to report findings as soon as they are found in the HackerOne platform alongside results from associated pentest engagements. The addition of Code Security Audit increases the depth of security coverage by providing the means to audit the security posture of DevOps practices.
In the past year, a specialized cohort of the HackerOne community, including a group of rigorously vetted, specialized software engineers and security experts, has performed over 30,000 code reviews. Each review takes a median of 88 minutes to complete and surfaces an average of 1.2 vulnerabilities.
Vulnerabilities that are most likely to be discovered in a code security audit:
- Design flaws and logic errors: Code audits can uncover design flaws and logic errors that might not be immediately apparent during production testing.
- Insecure coding practices: Input validation and output encoding issues, lack of proper error handling, inadequate access controls, and other insecure coding practices can lead to various attacks, including injection attacks, cross-site scripting (XSS), and privilege escalation.
- Hidden backdoors and malicious code: These are sometimes intentionally or unintentionally inserted into the codebase and are often difficult to detect through traditional production testing methods alone.
- Insecure dependencies: Code audits that include software composition analysis (SCA) can easily uncover vulnerabilities in third-party libraries and dependencies that the application might use.
- Sensitive data leakage: Data such as hard-coded credentials, API keys, or encryption keys are often stored insecurely within the code.
- Unintended information disclosure: Sensitive information — such as debug information, comments, or metadata — might unintentionally leak details about the application’s internals and infrastructure.
- Cryptographic vulnerabilities: Security vulnerabilities related to cryptography — such as weak encryption algorithms, improper key management, and insecure random number generation — are more likely to be found during a code audit due to their code-centric nature.
- Application and Infrastructure-as-Code misconfigurations: These might lead to security vulnerabilities such as incorrect and missing security settings, default configurations, or insecure cloud configurations.
Save Money
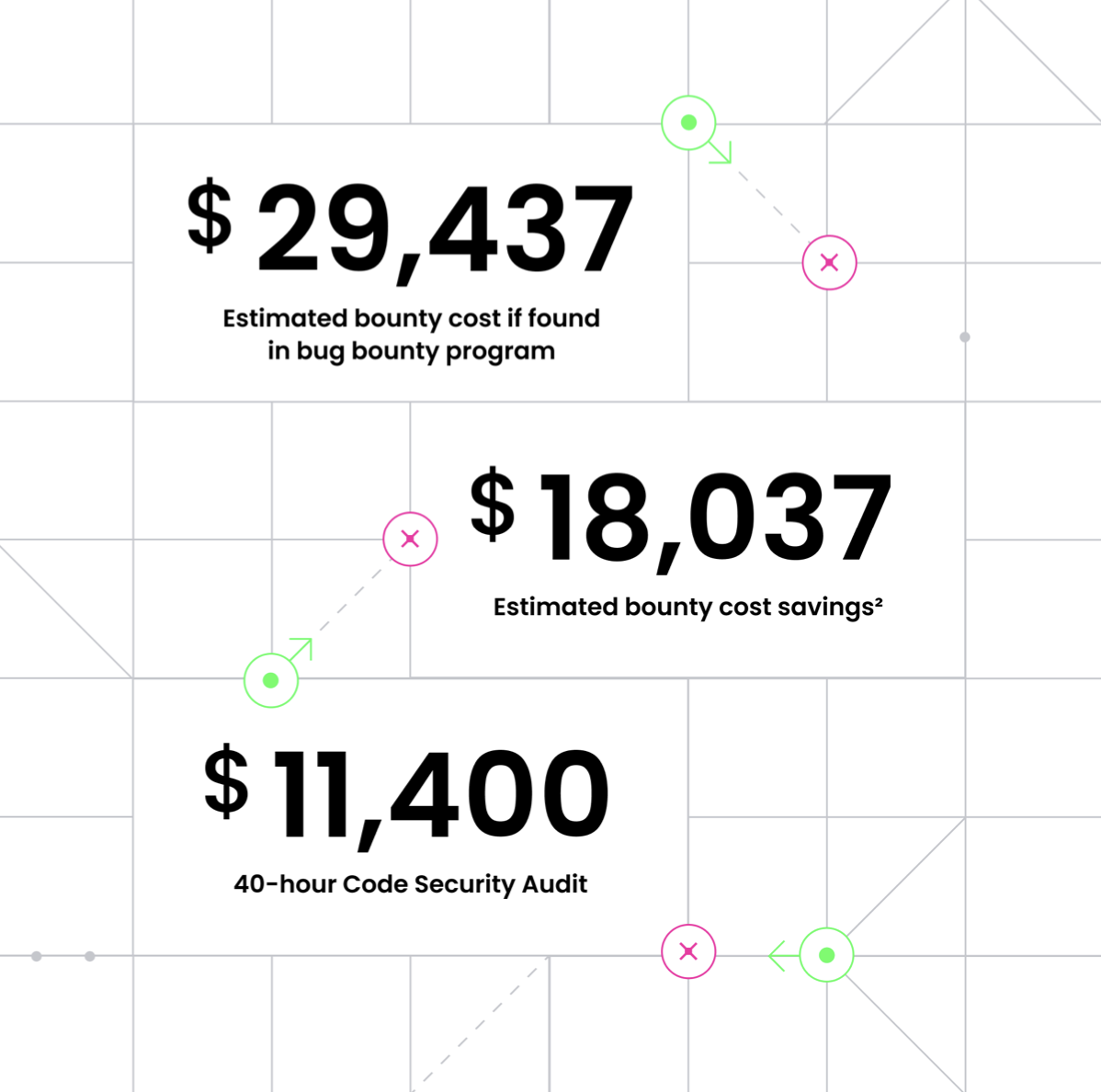
According to HackerOne’s 7th Annual Hacker Powered Report, the cost of a code security audit ($11,400) is considerably less expensive than the median bounty reward of HackerOne programs ($29,437 for an average of 24 bugs with a normal distribution of severity ratings). So? Finding mistakes earlier not only results in more secure code, but it also saves organizations money ($18,037).
To learn more about the power of incorporating Code Security Audit into your DevOps security, download the 7th Annual Hacker Powered Security Report. And to start finding vulnerabilities earlier and saving money with Code Security Audit, contact the team at HackerOne today.
Support Techcratic
If you find value in our blend of original insights (Techcratic articles and Techs Got To Eat), up-to-date daily curated articles, and the extensive technical work required to keep everything running smoothly, consider supporting Techcratic with Bitcoin. Your support helps me, as a solo operator, continue delivering high-quality content while managing all the technical aspects, from server maintenance to future updates and improvements. I am committed to continually enhancing the site and staying at the forefront of trends to provide the best possible experience. Your generosity and commitment are deeply appreciated. Thank you!
Bitcoin Address:
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge
Please verify this address before sending any funds to ensure your donation is directed correctly.
Bitcoin QR Code
Your contribution is vital in supporting my efforts to deliver valuable content and manage the technical aspects of the site. To donate, simply scan the QR code below. Your generosity allows me to keep providing insightful articles and maintaining the server infrastructure that supports them.

Privacy and Security Disclaimer
- No Personal Information Collected: We do not collect any personal information or transaction details when you make a donation via Bitcoin. The Bitcoin address provided is used solely for receiving donations.
- Data Privacy: We do not store or process any personal data related to your Bitcoin transactions. All transactions are processed directly through the Bitcoin network, ensuring your privacy.
- Security Measures: We utilize industry-standard security practices to protect our Bitcoin address and ensure that your donations are received securely. However, we encourage you to exercise caution and verify the address before sending funds.
- Contact Us: If you have any concerns or questions about our donation process, please contact us via the Techcratic Contact form. We are here to assist you.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.

















































![2024 Upgrade Tesla Model Y Sunshade Roof [Never Sag, No Gaps, Nano Ice-Crystal Coatings]…](https://techcratic.com/wp-content/uploads/2024/11/61USyoncEvL._AC_SL1500_-360x180.jpg)









![Japanese Movie – The X From Outer Space (Uchu Dai Kaijyu Girara) [Japan BD] SHBR-263](https://techcratic.com/wp-content/uploads/2024/11/81rV3BDVGJL._SL1024_-360x180.jpg)








