Sean Ryan
2023-06-01 18:00:00
www.hackerone.com
Use Code Security Audit for DevOps
DevOps teams may care about security, but it is not their area of expertise and it is not a priority for their pipeline goals. Adding security into the DevOps process adds friction and is difficult to get right, often taking years of trial and error for the early movers. GitLab’s Global DevSecOps Survey found that while over half of security teams are shifting left, 43% of security pros feel “somewhat” or “very” unprepared for the future.
Consider this common scenario: an application development team is under pressure to release a new version of a mobile consumer banking app to address poor user experience and customer churn. Security is important to the organization, so they run static code application security testing (SAST) scans, fix the issues they deem to be critical, perform internal peer code reviews, run through QA testing, stage the app, and finally release it into production. The mobile app is live, but how secure is it?
The IT Security team, which is not embedded in the software development lifecycle (SDLC), needs to be sure that the mobile app is not susceptible to account takeover, remote code injection, cross-site scripting, and more. The security team then runs a pentest to ensure compliance and security coverage, and includes the mobile app in its continuous bug bounty program to discover more elusive vulnerabilities. Meanwhile, the CISO who’s responsible for keeping mobile banking customers safe from cybercriminals is concerned about the high likelihood of critical vulnerabilities in the source code of the mobile app.
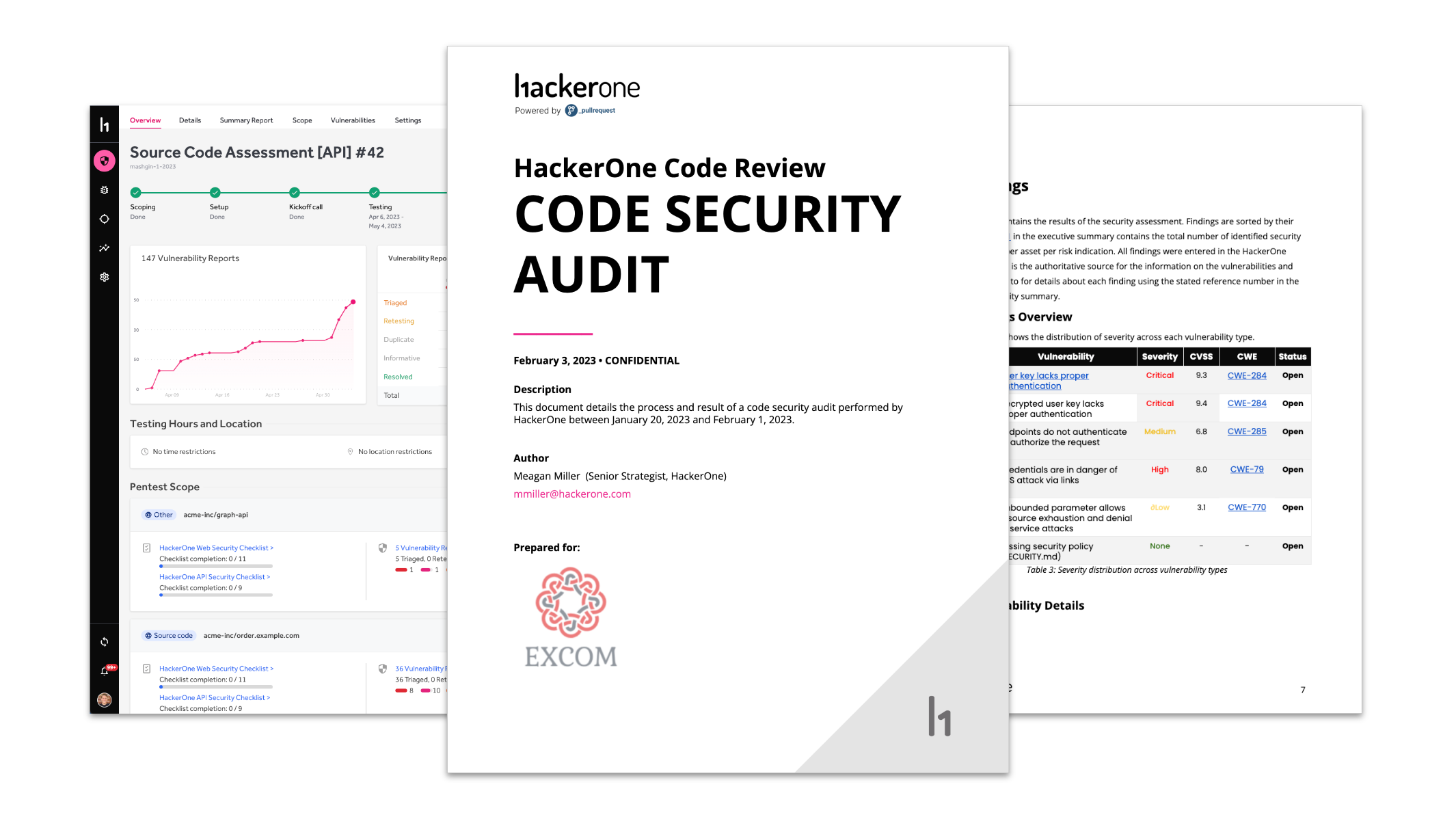
HackerOne Code Security Audit provide a means for the CISO in this scenario to address the concern about critical vulnerabilities by leveraging a community of vetted, expert code reviewers to report findings as soon as they are found in the HackerOne platform alongside results from associated pentest engagements. HackerOne’s Pentest as a Service (PTaaS) engagements support many assessment types, including web, mobile, AWS cloud, APIs, and external networks. The addition of Code Security Audit adds depth to security coverage by giving them the means to audit the security posture of DevOps practices.
Identify Risks in Code with Expert Reviewers
Experienced, expert human code reviewers uncover critical vulnerabilities that SAST scans miss, avoid false positives, and understand the context in order to provide specific, situational guidance for remediation.
An average of 37 medium to critical vulnerabilities are discovered in initial repository reviews by HackerOne’s code reviewers.
Some key capabilities include:
- Breadth of Security – All common programming languages, frameworks, and platforms are supported.
- Depth of Security – Reviewers apply a comprehensive approach, aided by a combination of HackerOne’s homegrown automation engine and internal technical experts, which work to capture key data to fast-track the review process and maximize reviewer time spent on the most important and high-risk areas of the code base.
- Operational Efficiency – Reviewers can integrate into your team’s existing code review processes and pipelines. Software integrations with CI/CD tools lead to faster and more effective remediation.
- Verified Reviewers – Our exclusive community of over 600 background-checked , vetted engineers typically have 5+ years of application security and engineering management experience. We adhere to strict NDA and PIIA protections.
Secure Integrations and Controls
The Code Security Audit solution supports all major source control providers, both cloud and self-hosted, with integrations to GitHub, GitLab, Azure DevOps, Bitbucket, and others. The solution is managed with the same controls as any other CI/CD tools in use.
Since source code review is a form of white box testing, we take access control and identity governance very seriously. As such, we provide granular access control, enforce least privilege access to code, provide full audit logs, and include single sign-on for developers and security teams.
A Key Addition to the HackerOne Attack Resistance Platform
HackerOne Pentest, along with the new Code Security Audit, is an integral capability of our Attack Resistance Platform. By unlocking the value of our community of security researchers to do reconnaissance and risk ranking on assets, along with both continuous and formalized security testing, you can help make meaningful gains in closing the security gaps in your attack surface.
To learn more about HackerOne Code Security Audit reach out to us directly for more information.
Support Techcratic
If you find value in our blend of original insights (Techcratic articles and Techs Got To Eat), up-to-date daily curated articles, and the extensive technical work required to keep everything running smoothly, consider supporting Techcratic with Bitcoin. Your support helps me, as a solo operator, continue delivering high-quality content while managing all the technical aspects, from server maintenance to future updates and improvements. I am committed to continually enhancing the site and staying at the forefront of trends to provide the best possible experience. Your generosity and commitment are deeply appreciated. Thank you!
Bitcoin Address:
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge
Please verify this address before sending any funds to ensure your donation is directed correctly.
Bitcoin QR Code
Your contribution is vital in supporting my efforts to deliver valuable content and manage the technical aspects of the site. To donate, simply scan the QR code below. Your generosity allows me to keep providing insightful articles and maintaining the server infrastructure that supports them.

Privacy and Security Disclaimer
- No Personal Information Collected: We do not collect any personal information or transaction details when you make a donation via Bitcoin. The Bitcoin address provided is used solely for receiving donations.
- Data Privacy: We do not store or process any personal data related to your Bitcoin transactions. All transactions are processed directly through the Bitcoin network, ensuring your privacy.
- Security Measures: We utilize industry-standard security practices to protect our Bitcoin address and ensure that your donations are received securely. However, we encourage you to exercise caution and verify the address before sending funds.
- Contact Us: If you have any concerns or questions about our donation process, please contact us via the Techcratic Contact form. We are here to assist you.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.














































![2024 Upgrade Tesla Model Y Sunshade Roof [Never Sag, No Gaps, Nano Ice-Crystal Coatings]…](https://techcratic.com/wp-content/uploads/2024/11/61USyoncEvL._AC_SL1500_-360x180.jpg)










![Japanese Movie – The X From Outer Space (Uchu Dai Kaijyu Girara) [Japan BD] SHBR-263](https://techcratic.com/wp-content/uploads/2024/11/81rV3BDVGJL._SL1024_-360x180.jpg)









