HackerOne
2021-05-03 15:00:00
www.hackerone.com
App Security is More Vital than Ever
The number of apps that organizations and individuals interact with has exploded over the last several years, creating an expansive landscape to make and keep safe. According to IDC, in the five years between 2018 and 2023, 500 million new digital apps and services will be created, equal to the number built over the past 40 years. But how are companies scaling their risk assessment approach to accommodate not only the sheer volume of apps but the diversity of environments they live in?
A few weeks ago, HackerOne and PortSwigger teamed up to shine a light on the innovative ways that customers and security analysts are approaching this problem. We heard from Leanne Shapton, Application Security Engineer at Shopify, and learned how she and her team are leveraging Portswigger’s Burp Suite scanning technology to quickly find security issues across its 6,000+ partner web apps — apps hosted largely in the cloud. We then heard from Joel Noguera, ethical hacker and pentester, who took us through the way he leverages the automation of Burp Suite to filter out the most obvious vulnerabilities so that he can hone in on critical, never-before-seen vulnerabilities that are often the favored vectors for malicious actors.
We asked the audience, “What form of security testing does your organization prioritize?” 51% answered automation before manual testing with 8% doing automation only.
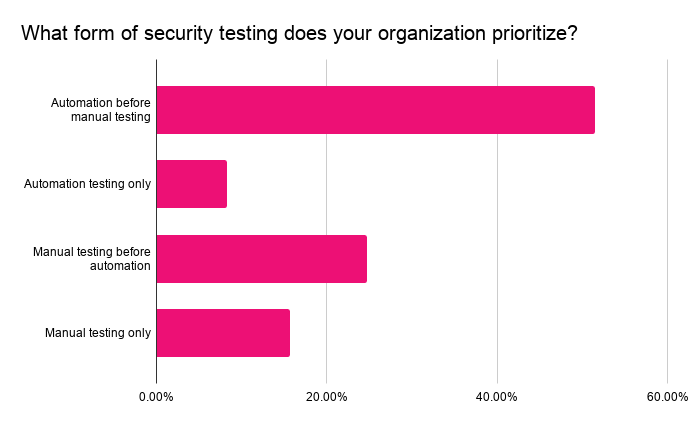
Most organizations today prioritize automation, but it’s not the end game. The value of automation is not necessarily what you get from scanning outputs, but what you decide to do with it. However, knowing where automation ends and manual testing begins isn’t obvious.
“If we don’t do enough automation, we’ll miss information from Burp Suite, its extensions, and active scans that can be generated in the background,” said Joel Noguera. “But when we do too much automation, we’ll produce predictable values and find the same bugs everyone is finding.”
Finding the balance and prioritization of what type of security testing should be implemented and when is a consistent challenge we hear from customers.
Automation + Expert Humans
For applications security teams, knowing the most effective methods for assessing risk should mean blending two critical disciplines. We heard loud and clear from both Leanne and Joel that combining the benefits of automated vulnerability scanning and human powered security testing delivers more protection than either one on its own. A best in class vulnerability scanning solution like Burp Suite can winnow out the majority of issues. From there, security experts can deep-dive on specific issues to determine severity levels and design a remediation plan, saving precious time.

Another poll for the audience was “What do you see as the benefits of automation?” Around 50% of the audience responded that automation is used to catch low hanging fruit while focusing different testing programs like pentests and bug bounty on critical vulnerabilities. Just 6% mentioned not having any automation in place today.
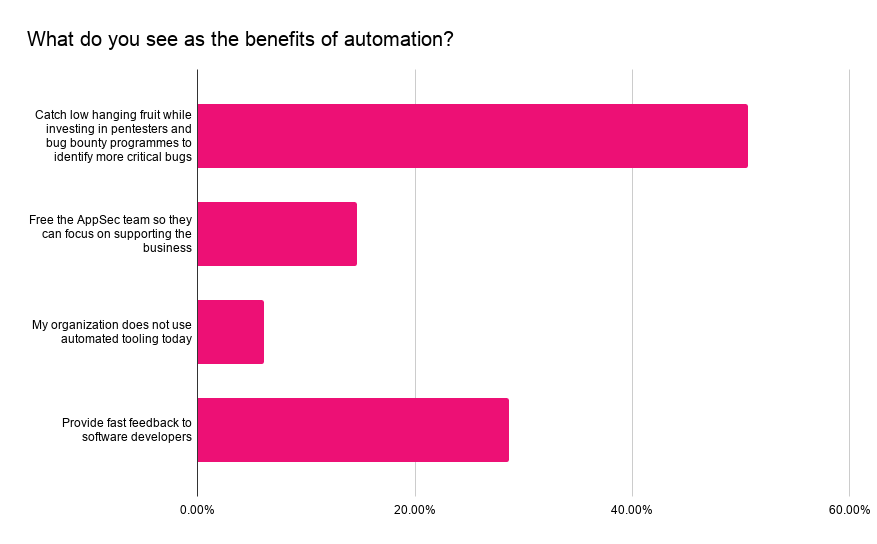
There is consistency from how audience members responded compared to the earlier question. The main benefit called out here is the ability to focus testing efforts on different types of vulnerabilities. Similarly, Leanne mentioned the importance of having a tiered security review process at Shopify based on the criticality of the service and context to the business.
“We run our own pentest on our critical services and we run a bug bounty through HackerOne – particularly good for code shipped frequently,” said Leanne Shapton. “Whereas pentests are moment in time and require manual effort, our bug bounty program is continuous. We have a great group of hackers who can continuously check the code we’re shipping out.”
Bringing together automated vulnerability scanning and human expertise is the best of both worlds for your ongoing app security strategy. It enhances the output and productivity of all the teams involved. Continual app security assessments fueled by automation and expertise are critical to an organization’s overall security posture, enabling teams to confidently deliver trusted customer experiences and innovative new products while maintaining compliance.
Want to learn more? Check out the on demand webinar, “How to Perform Effective Security Assessments.”
Keep your files stored safely and securely with the SanDisk 2TB Extreme Portable SSD. With over 69,505 ratings and an impressive 4.6 out of 5 stars, this product has been purchased over 8K+ times in the past month. At only $129.99, this Amazon’s Choice product is a must-have for secure file storage.
Help keep private content private with the included password protection featuring 256-bit AES hardware encryption. Order now for just $129.99 on Amazon!
Help Power Techcratic’s Future – Scan To Support
If Techcratic’s content and insights have helped you, consider giving back by supporting the platform with crypto. Every contribution makes a difference, whether it’s for high-quality content, server maintenance, or future updates. Techcratic is constantly evolving, and your support helps drive that progress.
As a solo operator who wears all the hats, creating content, managing the tech, and running the site, your support allows me to stay focused on delivering valuable resources. Your support keeps everything running smoothly and enables me to continue creating the content you love. I’m deeply grateful for your support, it truly means the world to me! Thank you!
|
BITCOIN
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge Scan the QR code with your crypto wallet app |
|
DOGECOIN
D64GwvvYQxFXYyan3oQCrmWfidf6T3JpBA Scan the QR code with your crypto wallet app |
|
ETHEREUM
0xe9BC980DF3d985730dA827996B43E4A62CCBAA7a Scan the QR code with your crypto wallet app |
Please read the Privacy and Security Disclaimer on how Techcratic handles your support.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.













































![[01_Odyssey] Generative art Exhibition – Dark Room Experience](https://techcratic.com/wp-content/uploads/2025/09/1756818266_maxresdefault-360x180.jpg)


























































