Aman Mishra
2025-02-26 15:07:00
gbhackers.com
Recent cybersecurity investigations have uncovered a sophisticated technique employed by threat actors to evade detection during malware distribution.
Attackers are leveraging ephemeral port 60102, typically reserved for temporary communications, as a service port for covert malware transmission.
This approach bypasses traditional monitoring systems, which often focus on scanning standard service ports such as 80 or 443.
Unconventional Port Usage in Malware Distribution
The attack begins with a successful password-guessing attempt, granting attackers access to a target system.
Once inside, the malicious actor executes commands to download malware from a remote server via HTTP using port 60102.
Tools like curl, wget, and direct TCP connections are employed to ensure the payload is retrieved, even if one method fails.
The server hosting the malwareidentified as an IP address based in Shanghai and owned by Tencent Cloud Computing Co., Ltd. has remained undetected by automated scanning tools like Shodan and GreyNoise due to its use of this nonstandard port.


Challenges in Detection and Mitigation
The use of ephemeral ports for HTTP traffic poses significant challenges for cybersecurity professionals.
Automated scanners like Shodan typically scan a predefined list of ports, which does not include port 60102.
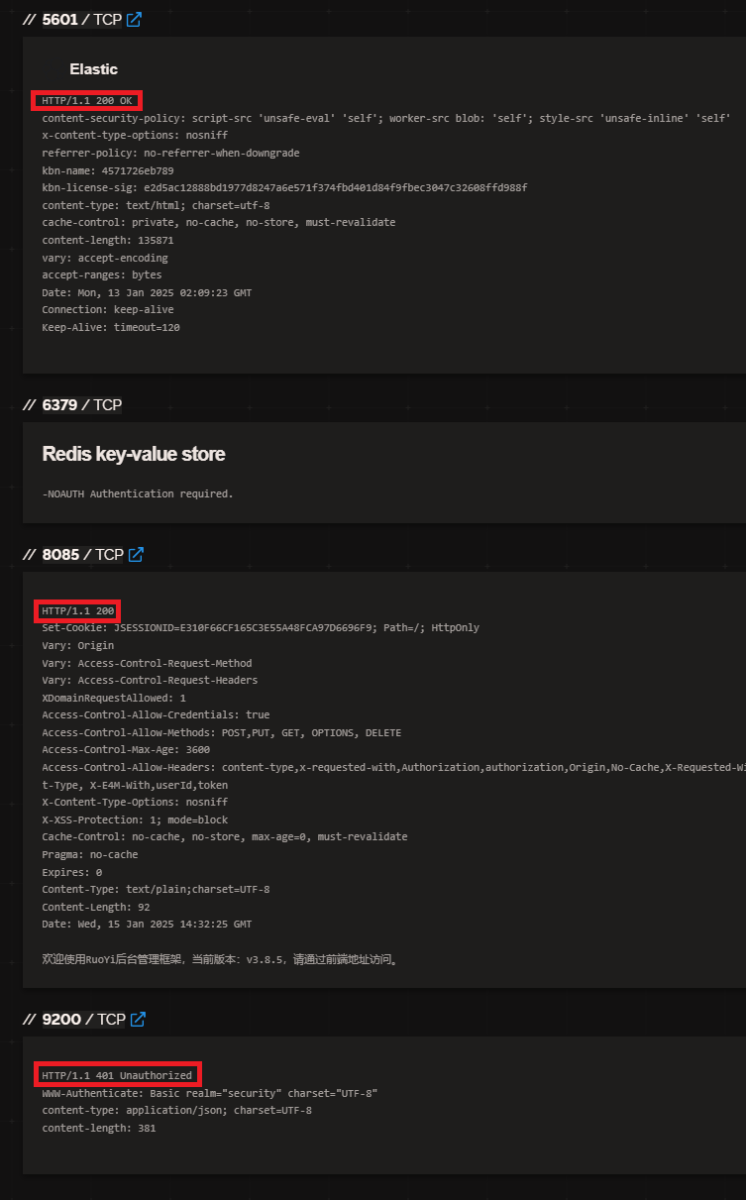
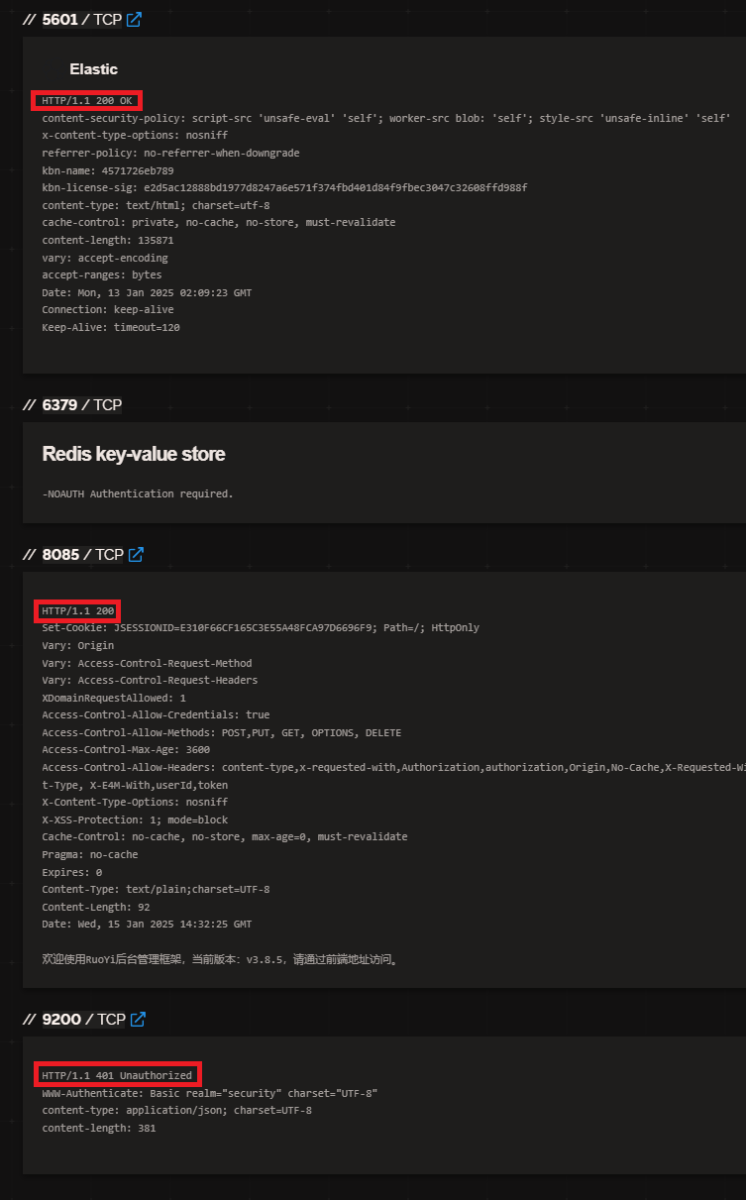
Similarly, GreyNoise relies on honeypots to detect malicious activity but may not capture attacks targeting specific systems.
According to ISC, this gap in detection allows threat actors to operate under the radar, using these ephemeral ports as temporary conduits for malware distribution.
Analysis of the attack revealed that the malicious server does not exhibit continuous malicious behavior but serves as a passive repository for malware files.
This intermittent activity further complicates identification and classification efforts.
Additionally, the use of nonstandard ports suggests that attackers have customized their infrastructure to evade conventional detection mechanisms.
To counter this emerging threat, organizations should implement robust security measures:
- Restrict Network Traffic: Limit inbound and outbound connections to authorized addresses and block HTTP traffic over unconventional ports like 60102.
- Enhance Credential Security: Enforce strong password policies, remove unused accounts, and disable root login via SSH to mitigate brute force attacks.
- Monitor Anomalous Connections: Use intrusion detection systems (IDS) or intrusion prevention systems (IPS) to flag unusual protocol-port pairings. Tools like Censys’s Universal Internet DataSet can aid in identifying nonstandard port usage.
- File Download Monitoring: Track file downloads from untrusted sources and inspect encrypted traffic where possible.
While these measures can mitigate current threats, the increasing use of ephemeral ports for malicious purposes underscores the need for continuous vigilance.
Cybersecurity professionals must adapt their strategies and leverage advanced tools to detect and respond to such sophisticated tactics effectively.
Collect Threat Intelligence on the Latest Malware and Phishing Attacks with ANY.RUN TI Lookup -> Try for free
Keep your files stored safely and securely with the SanDisk 2TB Extreme Portable SSD. With over 69,505 ratings and an impressive 4.6 out of 5 stars, this product has been purchased over 8K+ times in the past month. At only $129.99, this Amazon’s Choice product is a must-have for secure file storage.
Help keep private content private with the included password protection featuring 256-bit AES hardware encryption. Order now for just $129.99 on Amazon!
Help Power Techcratic’s Future – Scan To Support
If Techcratic’s content and insights have helped you, consider giving back by supporting the platform with crypto. Every contribution makes a difference, whether it’s for high-quality content, server maintenance, or future updates. Techcratic is constantly evolving, and your support helps drive that progress.
As a solo operator who wears all the hats, creating content, managing the tech, and running the site, your support allows me to stay focused on delivering valuable resources. Your support keeps everything running smoothly and enables me to continue creating the content you love. I’m deeply grateful for your support, it truly means the world to me! Thank you!
|
BITCOIN
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge Scan the QR code with your crypto wallet app |
|
DOGECOIN
D64GwvvYQxFXYyan3oQCrmWfidf6T3JpBA Scan the QR code with your crypto wallet app |
|
ETHEREUM
0xe9BC980DF3d985730dA827996B43E4A62CCBAA7a Scan the QR code with your crypto wallet app |
Please read the Privacy and Security Disclaimer on how Techcratic handles your support.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.
























































![SABRENT [3-Pack 22AWG Premium 6ft USB-C to USB A 3.0 Sync and Charge Cables [Black]…](https://techcratic.com/wp-content/uploads/2025/08/81SQ13LNwfL._SL1500_-360x180.jpg)















































