Aman Mishra
2025-03-26 05:48:00
gbhackers.com
Security researchers have uncovered a new attack campaign by the North Korean state-sponsored APT group Kimsuky, also known as “Black Banshee.”
The group, active since at least 2012, has been observed employing advanced tactics and malicious scripts in their latest cyber espionage efforts targeting countries such as South Korea, Japan, and the United States.
The attack begins with a ZIP file containing four components: a VBScript, a PowerShell script, and two encoded text files.
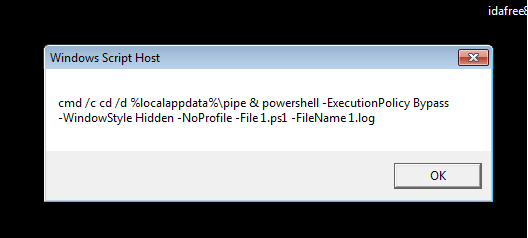
The VBScript utilizes obfuscation techniques, leveraging chr() and CLng() functions to dynamically generate characters and execute commands, effectively bypassing signature-based detection methods.
Multi-Stage Payload Analysis
Upon execution, the initial script triggers a PowerShell component that decodes base64-encoded data from one of the text files.
According to the Report, this decoded script performs several critical functions, including system reconnaissance, data exfiltration, and command-and-control (C2) communication.
The malware exhibits VM-aware behavior, terminating its execution if it detects a virtual machine environment.
For non-VM targets, it proceeds to collect sensitive information, including the BIOS serial number, which is used to create a unique directory for storing attack-related files.


Advanced Data Theft and Persistence Mechanisms
The Kimsuky malware demonstrates sophisticated capabilities for data exfiltration.
It targets multiple browsers, including Edge, Firefox, Chrome, and Naver Whale, to extract user profiles, cookies, login information, and web data.
The malware also searches for cryptocurrency wallet extensions and harvests their associated files.
Furthermore, the malware creates a comprehensive system profile, gathering hardware information, network adapter status, and a list of installed programs.
It implements persistence through scheduled tasks and continuously monitors the system for new data to exfiltrate.
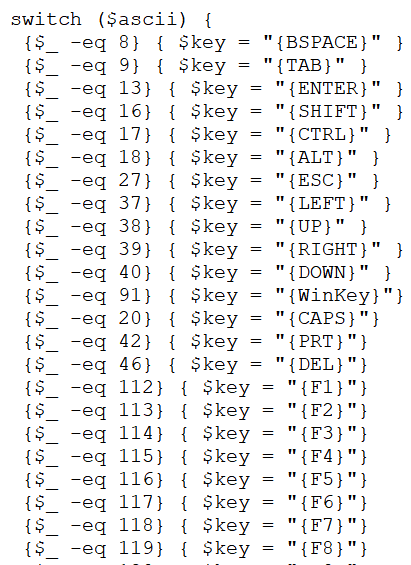
In the final stage of the attack, the malware deploys a keylogger component.
This module imports Windows API functions to detect key presses, monitor clipboard activity, and log window titles.


The collected data is periodically uploaded to the attacker’s C2 server, providing real-time surveillance of the victim’s activities.
The Kimsuky group’s evolving tactics and multi-component approach highlight the increasing sophistication of state-sponsored cyber threats.
As these attacks become more evasive and complex, organizations must remain vigilant and employ robust security measures to protect against such advanced persistent threats.
Are you from SOC/DFIR Teams? – Analyse Malware, Phishing Incidents & get live Access with ANY.RUN -> Start Now for Free.
Keep your files stored safely and securely with the SanDisk 2TB Extreme Portable SSD. With over 69,505 ratings and an impressive 4.6 out of 5 stars, this product has been purchased over 8K+ times in the past month. At only $129.99, this Amazon’s Choice product is a must-have for secure file storage.
Help keep private content private with the included password protection featuring 256-bit AES hardware encryption. Order now for just $129.99 on Amazon!
Help Power Techcratic’s Future – Scan To Support
If Techcratic’s content and insights have helped you, consider giving back by supporting the platform with crypto. Every contribution makes a difference, whether it’s for high-quality content, server maintenance, or future updates. Techcratic is constantly evolving, and your support helps drive that progress.
As a solo operator who wears all the hats, creating content, managing the tech, and running the site, your support allows me to stay focused on delivering valuable resources. Your support keeps everything running smoothly and enables me to continue creating the content you love. I’m deeply grateful for your support, it truly means the world to me! Thank you!
|
BITCOIN
bc1qlszw7elx2qahjwvaryh0tkgg8y68enw30gpvge Scan the QR code with your crypto wallet app |
|
DOGECOIN
D64GwvvYQxFXYyan3oQCrmWfidf6T3JpBA Scan the QR code with your crypto wallet app |
|
ETHEREUM
0xe9BC980DF3d985730dA827996B43E4A62CCBAA7a Scan the QR code with your crypto wallet app |
Please read the Privacy and Security Disclaimer on how Techcratic handles your support.
Disclaimer: As an Amazon Associate, Techcratic may earn from qualifying purchases.








































































































